FreeOTP
Jump to navigation
Jump to search
- Install oathtool
sudo apt-get install oathtool
- generate a random key
freddy@runner:~$ head -10 /dev/urandom | md5sum 5f0b169ad85959ddacc7fc1c28804ef9 -
WARNING: Generate your own KEY do not use this example!!
- Run oathtool to get the base32 version of the key
freddy@runner:~$ oathtool --totp --verbose 5f0b169ad85959ddacc7fc1c28804ef9 Hex secret: 5f0b169ad85959ddacc7fc1c28804ef9 Base32 secret: L4FRNGWYLFM53LGH7QOCRACO7E====== Digits: 6 Window size: 0 Step size (seconds): 30 Start time: 1970-01-01 00:00:00 UTC (0) Current time: 2019-09-04 15:24:00 UTC (1567610640) Counter: 0x31D53F8 (52253688) 125184
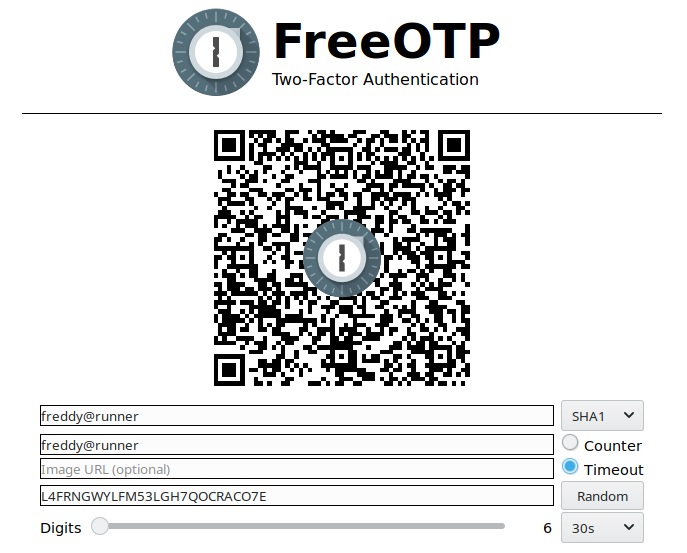
- go to https://freeotp.github.io/qrcode.html to create a QR code to load into the app (you could type the base32 key into the app directly but you'll never get it right). Put the "Base32 secret" from above into the fourth box. Ignore the "=" signs.
- open the app and scan the QRcode on the screen
That's just about it .... if you run "oathtool --totp 5f0b169ad85959ddacc7fc1c28804ef9" on the server, assuming you're closks are sync'd, it should match the numbers in the FreeOTP app.
Next step is to integrate that into LINUX PAM, using libpam-oath, or into your application using the other oath libraries out there.
- Other handy tools for debugging:
- https://cryptii.com/pipes/base32-to-hex base32 to hex encode / decode